
Threat actors have already started targeting Internet-exposed VMware vCenter servers unpatched against a critical arbitrary file upload vulnerability patched yesterday that could lead to remote code execution.
The security flaw tracked as CVE-2021-22005 impacts all vCenter Server 6.7 and 7.0 deployments with default configurations.
The flaw was reported by George Noseevich and Sergey Gerasimov of SolidLab LLC, and unauthenticated attackers can remotely exploit it in low complexity attacks without requiring user interaction.
Scanning starts hours after patch release
While exploit code is not yet publicly available, ongoing scanning activity was already spotted by threat intelligence company Bad Packets, with some of its VMware honeypots recording attackers probing for the presence of the critical bug just hours after VMware released security updates.
"CVE-2021-22005 scanning activity detected from 116[.]48.233.234," Bad Packets tweeted earlier today, later adding that the scans are using workaround information provided by VMware for customers who couldn't immediately patch their appliances.
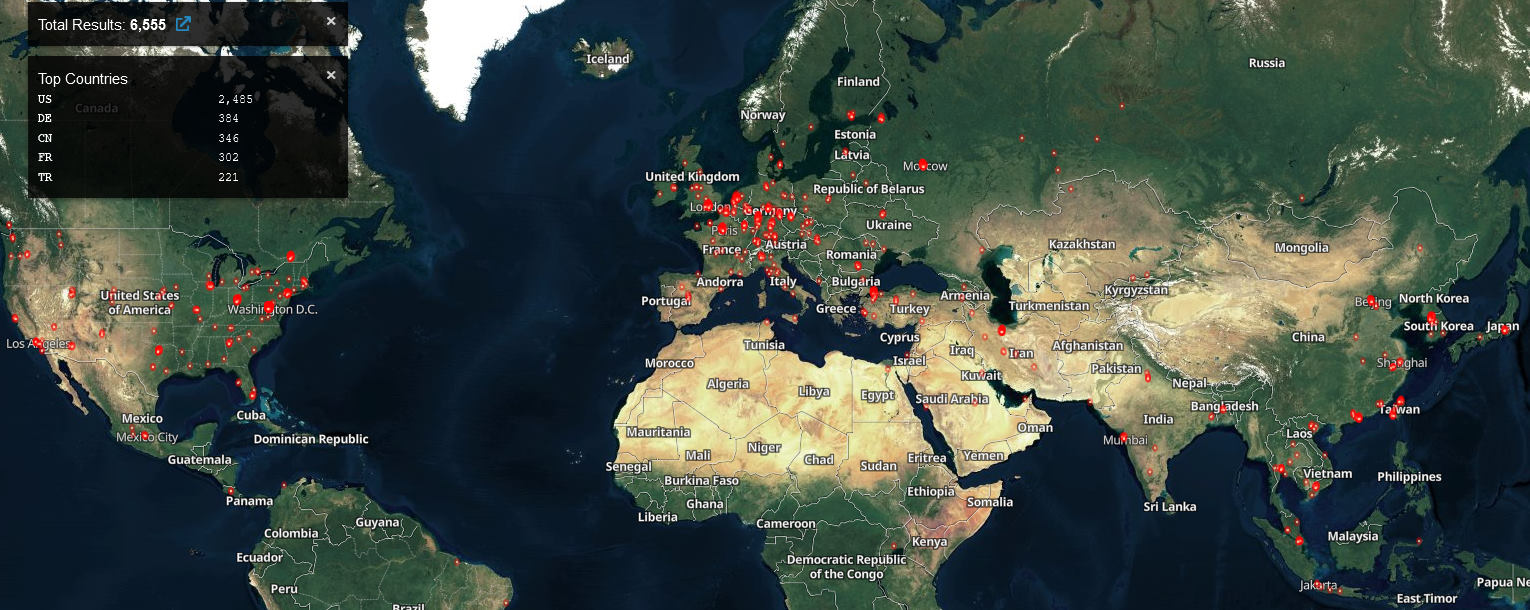
Right now, thousands of potentially vulnerable vCenter servers are reachable over the Internet and exposed to attacks, according to the Shodan search engine for Internet-connected devices.
This is not the first time threat actors have scanned for and attacked vulnerable VMware vCenter servers.
In February, attackers mass scanned for unpatched vCenter appliances after security researchers released proof-of-concept (PoC) exploit code for another critical RCE security flaw (CVE-2021-21972) impacting all default vCenter installs.
In June, scanning began for Internet-exposed VMware vCenter servers left vulnerable to CVE-2021-21985 RCE exploits after exploit code was published online.
VMware warns of incoming exploitation attempts
These ongoing scans follow a warning issued by VMware yesterday to highlight the importance of patching servers against the CVE-2021-22005 bug as soon as possible.
"This vulnerability can be used by anyone who can reach vCenter Server over the network to gain access, regardless of the configuration settings of vCenter Server," said Bob Plankers, Technical Marketing Architect at VMware.
"In this era of ransomware it is safest to assume that an attacker is already inside your network somewhere, on a desktop and perhaps even in control of a user account, which is why we strongly recommend declaring an emergency change and patching as soon as possible."
The company provides a workaround requiring admins to edit a text file on the virtual appliance and restarting services manually or using a script to remove the exploitation vector.
VMware also published a detailed FAQ document with additional questions and answers regarding the CVE-2021-22005 flaw.
"Immediately, the ramifications of this vulnerability are serious and it is a matter of time – likely minutes after the disclosure – before working exploits are publicly available," VMware added.
"With the threat of ransomware looming nowadays, the safest stance is to assume that an attacker may already have control of a desktop and a user account through the use of techniques like phishing or spearphishing and act accordingly.
"This means the attacker may already be able to reach vCenter Server from inside a corporate firewall, and time is of the essence."


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now