
Security researchers have identified a new data-wiping malware they named SwiftSlicer that aims to overwrite crucial files used by the Windows operating system.
The new malware was discovered in a recent cyberattack against a target in Ukraine and has been attributed to Sandworm, a hacking group working for Russia’s General Staff Main Intelligence Directorate (GRU) as part of the Main Center for Special Technologies (GTsST) military unit 74455.
Go-based data wiper
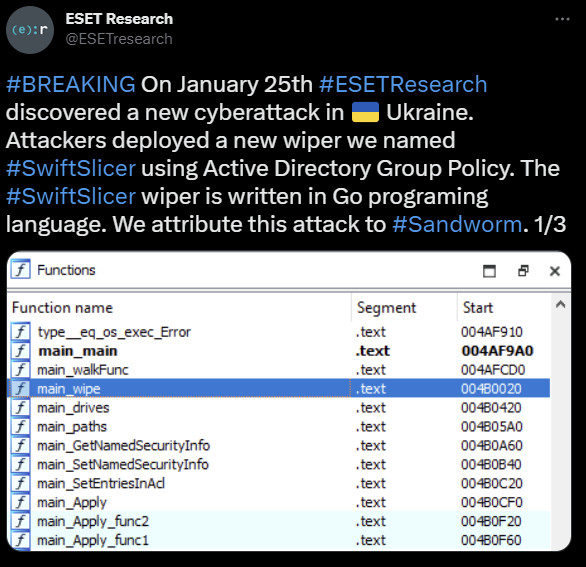
While details are scant regarding SwiftSlicer at the moment, security researchers at cybersecurity company ESET say that they found the destructive malware deployed during a cyberattack in Ukraine.
The name of the target has not been published, recent Sandworm activity includes a data-wiping attack on Ukrinform, Ukraine’s national news agency.
However, in the attack that ESET discovered on January 25 the threat actor launched a different destructive malware called CaddyWiper, previously observed in other attacks on Ukrainian targets [1, 2].
ESET says that Sandworm launched SwiftSlicer using Active Directory Group Policy, which allows domain admins to execute scripts and commands throughout all of the devices in Windows network.
ESET researchers say that SwiftSlicer was deployed to delete shadow copies and to overwrite critical files in the Windows system directory, specifically drivers and the Active Directory database.
The specific targeting of the %CSIDL_SYSTEM_DRIVE%\Windows\NTDS folder indicates that the wiper is not only meant to destroy files but to also bring down the entire Windows domains.
SwiftSlicer overwrites data using 4096 bytes blocks that are filled with randomly generated bytes. After completing the data destruction job, the malware reboots the systems, ESET researchers say.
According to the researchers, Sandworm developed SwiftSlicer in Golang programming language, which has been adopted by multiple threat actors for its versatility, and it can be compiled for all platforms and hardware.
Although the malware has been added to the Virus Total database only recently (submitted on January 26), it is currently detected by more than half of the antivirus engines present on the scanning platform.
Russia's destructive malware
In a report today, the Ukrainian Computer Emergency Response Team (CERT-UA) says that Sandworm also tried to use five data-destruction utilities on the Ukrinform news agency’s network:
- CaddyWiper (Windows)
- ZeroWipe (Windows)
- SDelete (legitimate tool for Windows)
- AwfulShred (Linux)
- BidSwipe (FreeBSD)
The agency’s investigation revealed that SandWorm distributed the malware to computers on the network using a Group Policy Object (GPO) - a set of rules administrators use to configure operating systems, apps, and user settings in an Active Directory environment, the same method also used to execute SwiftSlicer.









Comments
vic-t - 2 years ago
But what's the attack vector? You need domain admin rights to perform any of those actions. Meaning that an administrator with such privileges has to actively run the malware for something to happen. How likely is this if the infrastructure is professionally managed?
ThomasMann - 2 years ago
You are totally correct... it is always the same! Only in rare cases is the "infrastructure professionally managed".
Otherwise NONE of this garbage could be successful. The simple answer is: MOST of those so-called computer specialists are morons, the only reason why the have the job is, that basically NO computer user has the slightest idea how "this all" works. So they have to trust any incompetent idiot who makes thousands of dollars for absolutely mediocre work, because there is no one whó is able to control their work.
Users are not interested wasting their time in learning, they simply want to pay someone who fixes everything for them.
Just image people on the intelligence level of most computer programmers and security "experts" would work in medicine, or, simply be the ones that repair your car!
MisterVVV - 2 years ago
ThomasMann, are you a Computer specialist or?
Have a nice day
Best regards!
//me
EndangeredPootisBird - 2 years ago
Don't bother, he's just an troll.
deltasierra - 2 years ago
Definitely curious to see the attack chain on how they got to the point of deploying via GPO. If domain admin was compromised, they could destroy the domain in any number of ways. I suppose SandWorm figured their TTP's were stealthier and less likely to recover from? I don't know, IMO, domain admin privileges sound great for LoLbin attacks.