
As Twitter announces plans to charge users $8 a month for Twitter Blue and account verification under Elon Musk's management, BleepingComputer has come across multiple phishing emails targeting verified users.
Twitter business model shakeup draws scammers in
Earlier this week, Elon Musk appointed himself as Twitter's CEO and announced plans to revamp Twitter's verification process.As a part of this review, Twitter initially proposed to start charging verified users a $20 monthly fee. Later, Musk stated the fee would be dropped to $8.
Other than receiving a blue tick following successful verification, paid users are expected to get "priority in replies, mentions & search," fewer ads, and will be able to post longer multimedia content:
You will also get:
— Elon Musk (@elonmusk) November 1, 2022
- Priority in replies, mentions & search, which is essential to defeat spam/scam
- Ability to post long video & audio
- Half as many ads
Following Musk's tweets, BleepingComputer observed newer phishing campaigns emerging with threat actors now targeting verified accounts.
Like many phishing emails, these emails convey a false sense of urgency, urging the user to sign-in to their Twitter account or risk "suspension."
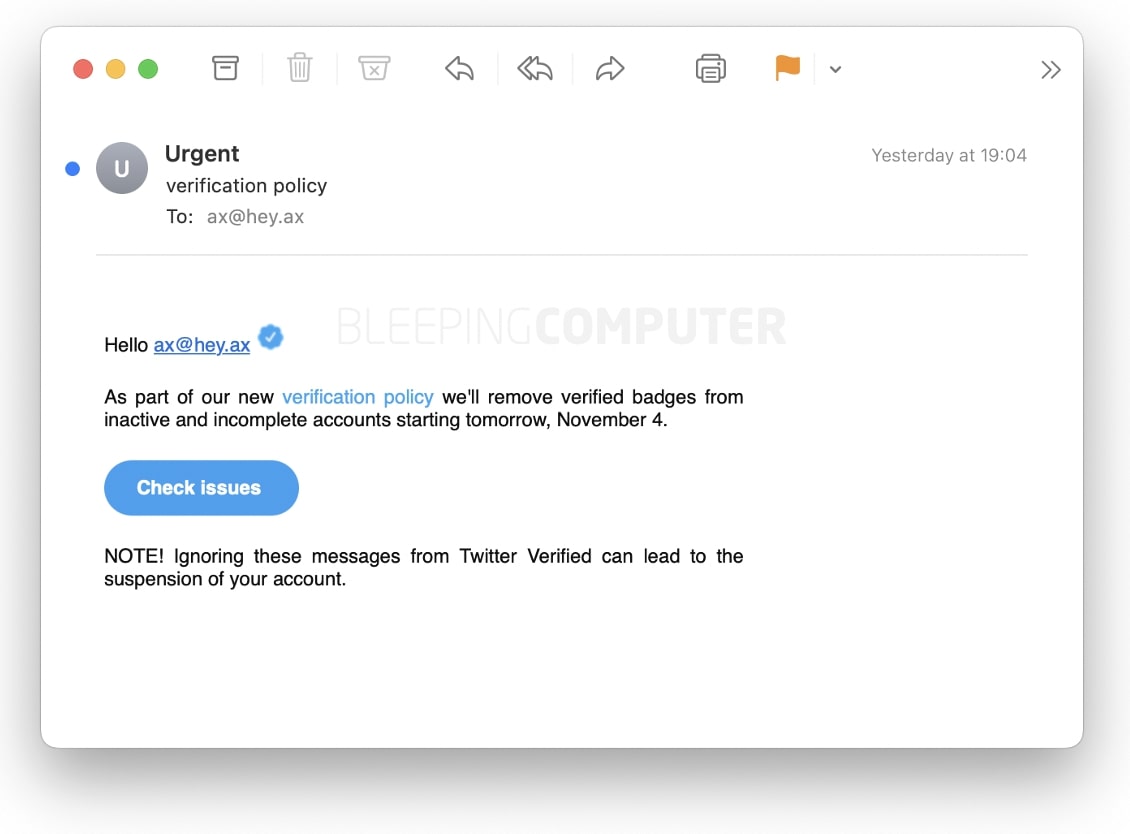
Analysis by BleepingComputer revealed these emails were originating from servers of hacked websites and blogs that may be, for example, hosting dated WordPress versions or running unpatched, vulnerable plugins.
Clicking on the link takes the user to the phishing webpage where threat actors misuse the $8 monthly fee announcement from Musk's tweets:
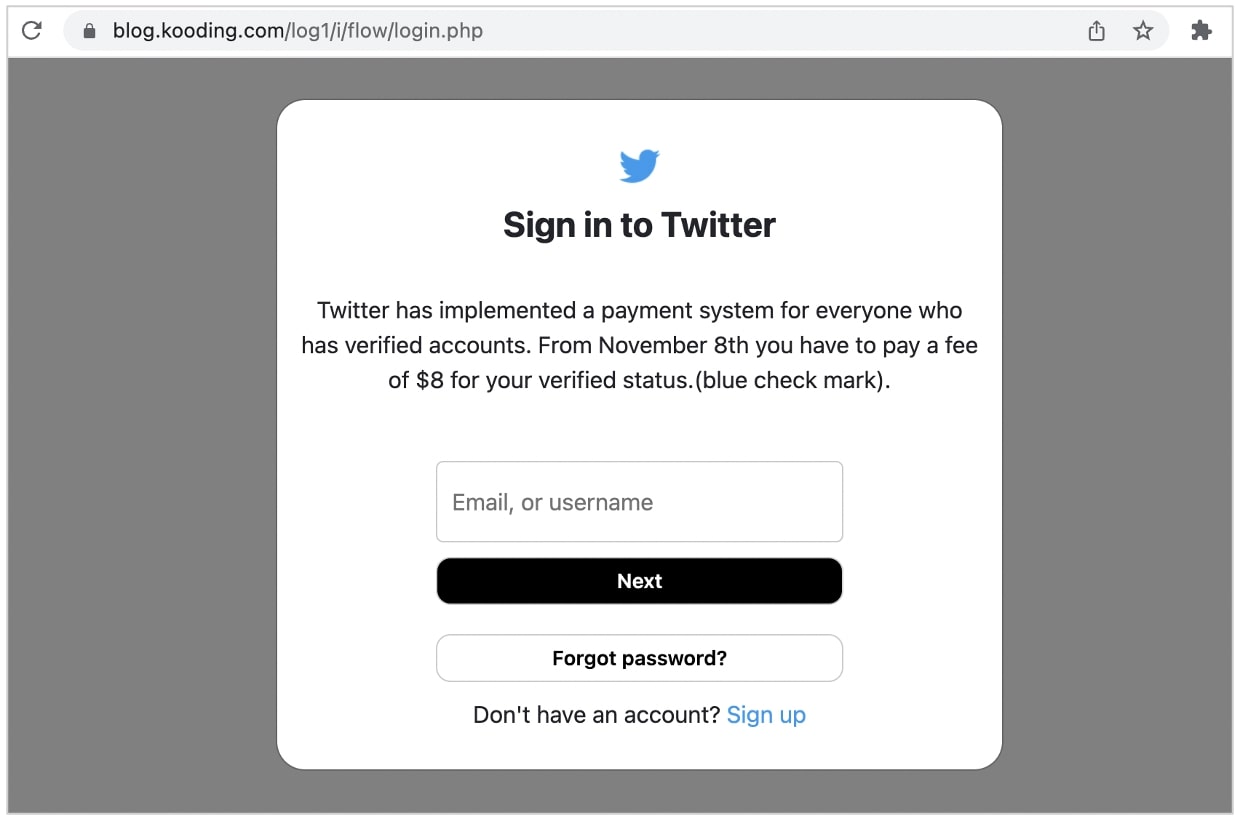
The phishing workflow collects user's Twitter username, password, and proceeds to sending them a two-factor authentication code via SMS.
A more convincing phishing message also received and analyzed by BleepingComputer is shown below:

This email incorporates identical wording to the phishing page itself and has an overall look-and-feel that is more akin to Twitter's branding.
Twitter verification: beyond vanity
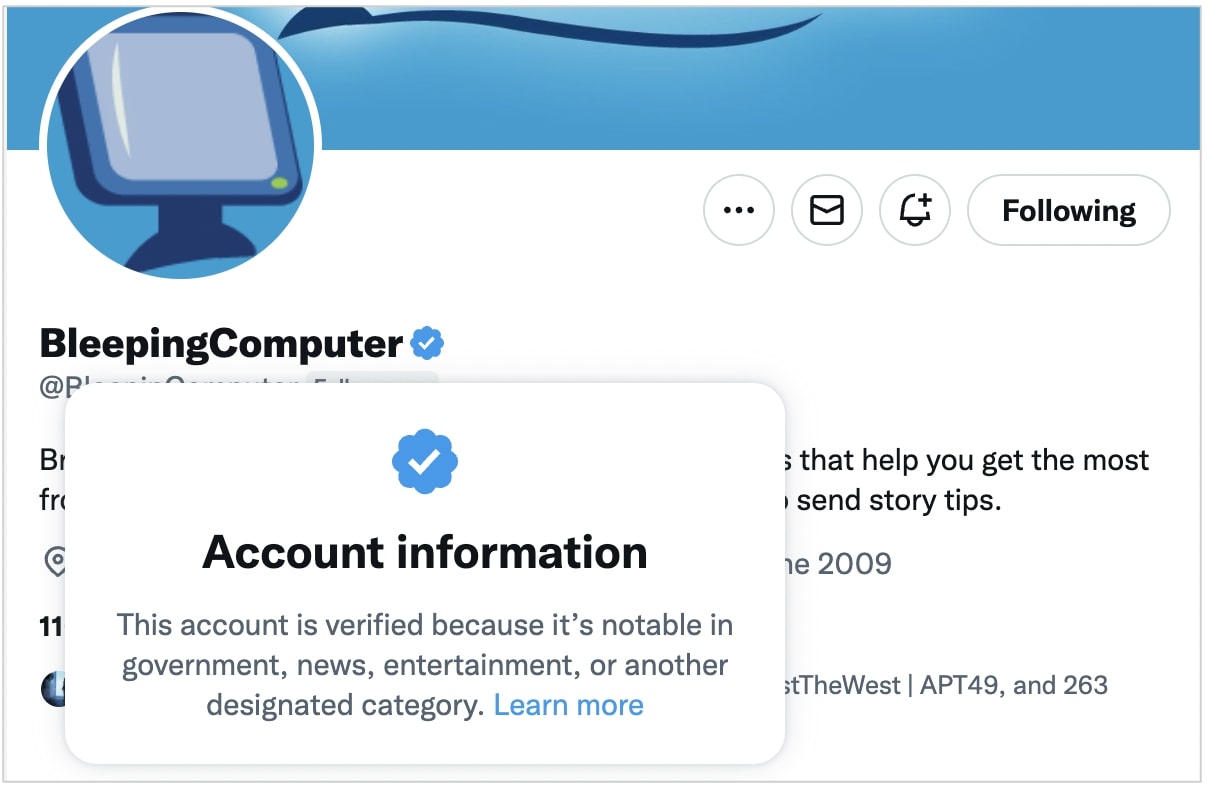
Twitter blue badge with a checkmark have traditionally been offered to verified accounts of politicians, celebrities, businesses, public figures, influencers, news organizations and journalists.
The scarcity of blue badge accounts on the platform, compared to the vast majority of Twitter's accounts that are unverified, has led to the "blue tick" being perceived by tweeters to be a vanity and status symbol.
Threat actors have also repeatedly targeted verified users via phishing, and sometimes hacked blue badge accounts to push crypto scams.
In other scams, threat actors have hacked verified accounts to impersonate another person to mislead the public or to send Twitter users fake 'account suspension' DMs.
Musk has dissed the existing verification process as "Twitter's current lords & peasants system."
However, other than its "status symbol" perception for some, the blue badge is primarily intended to separate real, authentic accounts of notable people from copycat and parody accounts created by third parties—at least in theory.
The verification is therefore intended to limit misinformation in the sense that users can see a tweet originating from a verified account is authentic and didn't originate from someone impersonating a public figure.
In practice, however, results can vary as a hacked 'verified' account may continue to retain the blue badge even if the hacker changes the name, bio and profile picture on it, thereby making the presence of the badge futile to begin with.
If the blue badge becomes commoditized and available to just about anyone willing to shed $8 a month, Twitter will need to rethink its process to add authenticity to notable accounts.
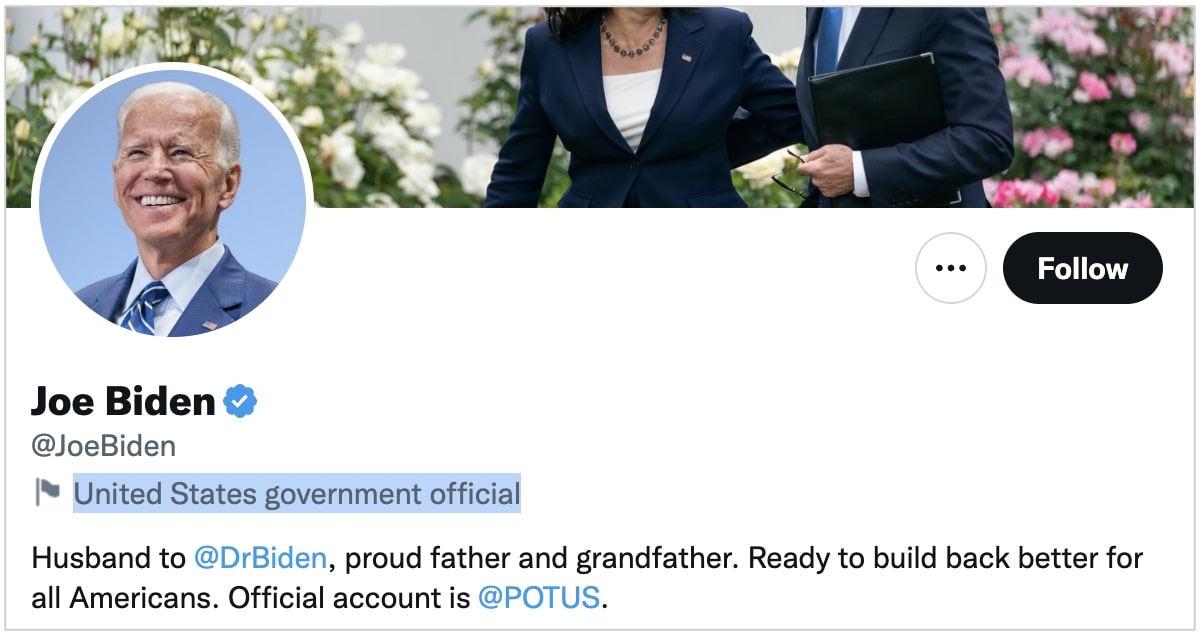
One of the ways to achieve this could be, for example, to continue the use special labels on Twitter accounts of politicians and state-affiliated entities, which then creates some distinction between authentic accounts of public figures and those with a paid blue badge.
Without a streamlined verification process that clearly separates authentic notable accounts from imposters, the problems of Twitter's existing verification sphere won't disappear anytime soon.








Comments
fromFirefoxToVivaldi - 2 years ago
If the first screenshot is how e-mails are displayed on Macs I'm no longer surprised people fall for obvious scams. Imagine creating an e-mail client and not even showing the sender's e-mail address. Is it even possible to view e-mail source and inspect headers on something this rudimentary?
h_b_s - 2 years ago
"If the first screenshot is how e-mails are displayed on Macs I'm no longer surprised people fall for obvious scams. Imagine creating an e-mail client and not even showing the sender's e-mail address. Is it even possible to view e-mail source and inspect headers on something this rudimentary? "
It's the default view and I'd imagine most people never bother to change it. They don't know/don't care to know how to read e'mail addresses to begin with - which is immaterial anyway. It's trivially easy to spoof the From: line in e'mail. Almost no one bothers to read the rest of the meta data enclosed in the header even if they know how to decode it. E'mail is a legacy system from an era in which security wasn't even a wet dream and there are no easy solutions to the problem especially once you involve largely incompetent politicians trying to create laws to regulate interop.
fromFirefoxToVivaldi - 2 years ago
It's not immaterial. 90% of phishing/scam/malware e-mails we get are from x@[obviousscam].porn/xyz/other TLD like that.
Properly implemented DMARC makes successful spoofing attempts impossible for any well managed domain.
KeiFeR123 - 2 years ago
I'll have to agree with this. I work as sysad in our organization. You'll be surprised how many legit organizations in private or government section that don't have DMARC implemented or properly implemented. Blows your mind.
fromFirefoxToVivaldi - 2 years ago
Then this must vary by country. In my country it's widely implemented and the government's CSIRT instructs organizations how to do this and also follows up if they notice successful spoofing attempts. Thus spoofing attempts are pretty much nonexistent as far as security goes, they might happen, but such messages will be discarded without anyone having to pay any attention.